
A previously undocumented Android spyware called ‘EagleMsgSpy’ has been discovered and is believed to be used by law enforcement agencies in China to monitor mobile devices.
According to a new report by Lookout, the spyware was developed by Wuhan Chinasoft Token Information Technology Co., Ltd. and has been operational since at least 2017.
Lookout presents abundant evidence linking EagleMsgSpy to its developers and operators, including IP addresses tied to C2 servers, domains, direct references in internal documentation, and also public contracts.
The researchers also found clues for the existence of an iOS variant. However, they have yet to gain access to a sample for analysis.
Powerful Android spyware
Lookout believes that law enforcement manually installs the EagleMsgSpy spyware when they have physical access to unlocked devices. This could be achieved by confiscating the device during arrests, something common in oppressive countries.
Lookout has not seen the installer APK on Google Play or any third-party app stores, so the spyware is presumably only distributed by a small circle of operators.

Source: Lookout
Subsequent versions of the malware sampled by the analysts show code obfuscation and encryption improvements, indicative of active development.
EagleMsgSpy’s data theft activities include targeting the following:
- Messages from chat apps (QQ, Telegram, WhatsApp, etc.)
- Screen recording, screenshots, and audio recordings.
- Call logs, contacts, SMS messages.
- Location (GPS), network activity, installed apps.
- Browser bookmarks, external storage files.
Data is stored temporarily in a hidden directory, encrypted, compressed, and exfiltrated to the command-and-control (C2) servers.
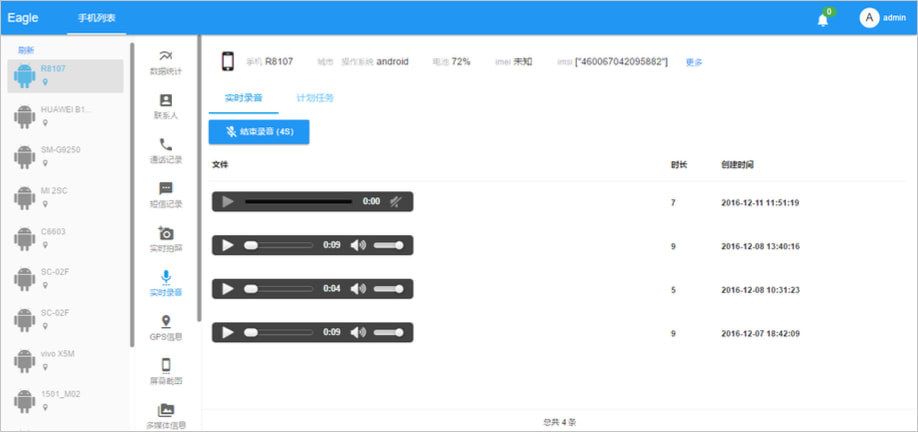
The malware features an administrator panel called “Stability Maintenance Judgment System.”
The panel allows remote operators to initiate real-time activities like triggering audio recordings or showing the target’s contacts’ geographical distribution and communication exchange.
Source: Lookout
Behind EagleMsgSpy
Lookout says with high confidence that the creators of EagleMsgSpy is Wuhan Chinasoft Token Information Technology, tied to the malware through overlaps in infrastructure, internal documentation, and OSINT investigations.
For example, a domain the company uses for promotional materials (‘tzsafe[.]com’) also appears in EagleMsgSpy’s encryption strings, while the malware’s documentation directly references the firm’s name.
Additionally, test device screenshots from the admin panel correspond to the location of the firm’s registered office in Wuhan.
Regarding the spyware operators, Lookout claims that C2 servers are tied to domains of public security bureaus, including the Yantai Public Security Bureau and its Zhifu Branch.
Historical IP records also show overlaps with domains used by bureaus in Dengfeng and Guiyang.
Finally, the name of the admin panel suggests that it’s systematically used by law enforcement or other government agencies.

