
A maximum severity vulnerability in the FreeScout helpdesk platform allows hackers to achieve remote code execution without any user interaction or authentication.
The flaw is tracked as CVE-2026-28289 and bypasses a fix for another remote code execution (RCE) security issue (CVE-2026-27636) that could be exploited by authenticated users with upload permissions.
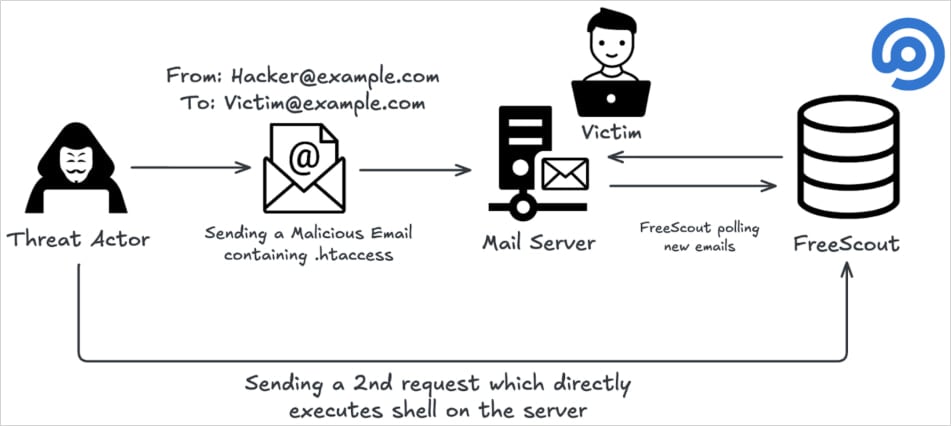
Researchers at OX Security, a company that secures applications from code to runtime, say that an attacker can exploit the new vulnerability by “sending a single crafted email to any address configured in FreeScout.”
According to them, the fix attempted to block dangerous file uploads by modifying filenames with restricted extensions or those starting with a dot.
The OX Research team discovered that a zero-width space (Unicode U+200B) could be placed before the filename to bypass the recently introduced validation mechanism, since the character is not treated as visible content.
Subsequent processing removes that character, allowing the file to be saved as a dotfile, and hence, still triggering CVE-2026-27636 exploitation by completely bypassing the latest security checks.
Source: OX Research
Making matters worse, CVE-2026-28289 can be triggered by a malicious email attachment delivered to a mailbox configured in FreeScout, the researchers say.
The program stores the attachment in “/storage/attachment/…,” enabling the attacker to access the uploaded payload through the web interface and execute commands on the server without authentication or user interaction, making it a zero-click vulnerability.
[embedded content]
“A patch bypass vulnerability in FreeScout 1.8.206 allows any authenticated user with file upload permissions to achieve Remote Code Execution (RCE) on the server by uploading a malicious .htaccess file using a zero-width space character prefix to bypass the security check,” the vendor says in a security bulletin.
FreeScout is an open-source help desk and shared mailbox platform used by organizations to manage customer support emails and tickets. It’s a self-hosted alternative to Zendesk or Help Scout.
The project’s GitHub repository has 4,100 stars and over 620 forks, and OX Research reports that its Shodan scans returned 1,100 publicly exposed instances, indicating it’s a widely used solution.
CVE‑2026‑28289 affects all FreeScout versions up to and including 1.8.206 and was patched in version 1.8.207, released four days ago.
The FreeScout team warned that successful exploitation of CVE‑2026‑28289 may result in full server compromise, data breaches, lateral movement into internal networks, and service disruption. Hence, immediate patching is advised.
OX Research has also recommended disabling ‘AllowOverrideAll’ in the Apache configuration on the FreeScout server, even when on version 1.8.207.
No active exploitation of CVE‑2026‑28289 has been observed in the wild as of writing this, but given the nature of this flaw, the danger of malicious activity starting soon is very high.


