
The FBI has seized two websites used by the Handala hacktivist group after the threat actors conducted a destructive cyberattack on medical technology giant Stryker that wiped approximately 80,000 devices.
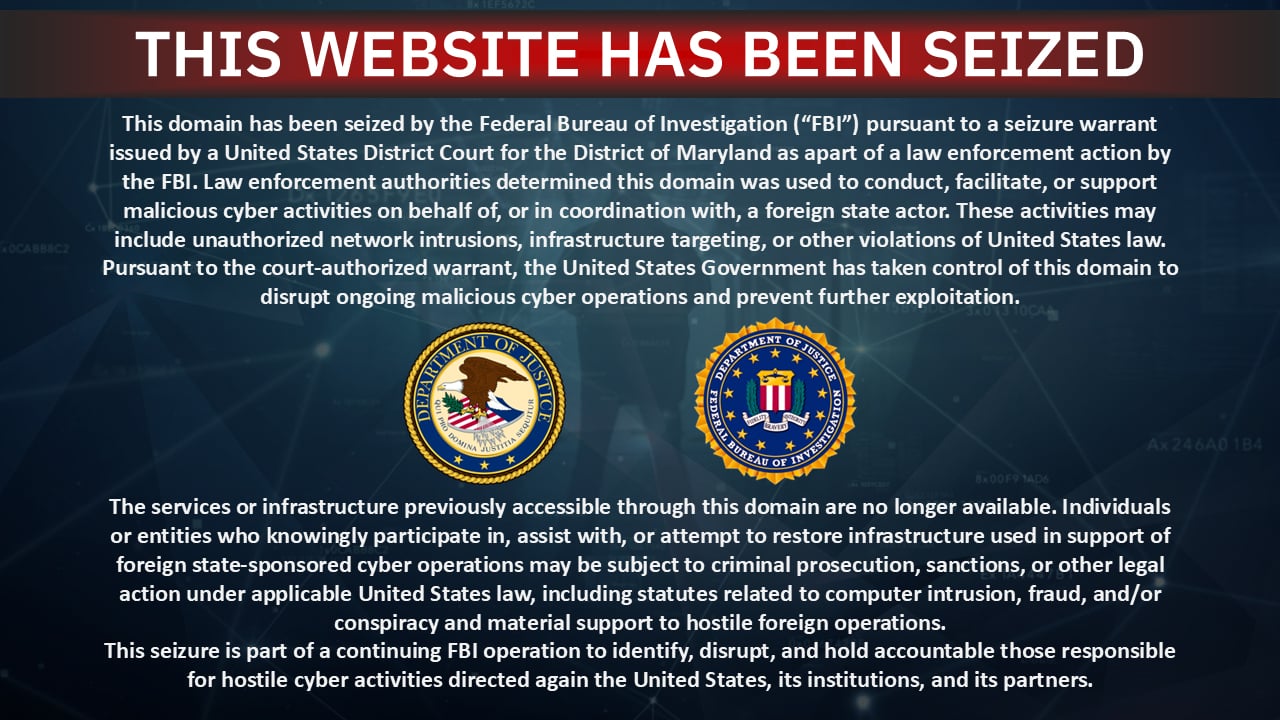
Both the hacktivist’s handala-redwanted[.]to and handala-hack[.]to clearnet domains now display a seizure notice stating that the websites were seized under a seizure warrant issued by the District Court for the District of Maryland.
“This domain has been seized by the Federal Bureau of Investigation (“FBI”) pursuant to a seizure warrant issued by a United States District Court for the District of Maryland as apart of a law enforcement action by the FBI. Law enforcement authorities determined this domain was used to conduct, facilitate, or support malicious cyber activities on behalf of, or in coordination with, a foreign state actor,” reads the seizure message.
“These activities may include unauthorized network intrusions, infrastructure targeting, or other violations of United States law.”
“Pursuant to the court-authorized warrant, the United States Government has taken control of this domain to disrupt ongoing malicious cyber operations and prevent further exploitation.”
Source: BleepingComputer
Handala (also known as Handala Hack Team, Hatef, Hamsa) is an Iranian-linked, pro-Palestinian hacktivist group that first appeared in December 2023, and conducted operations reportedly linked to Iran’s Ministry of Intelligence and Security (MOIS). These attacks targeted Israeli organizations with destructive malware designed to wipe Windows and Linux devices.
While there has been no official announcement by law enforcement regarding the seizures, the domain name servers have now been switched to those commonly used by the FBI when seizing domains:
Name Server: ns1.fbi.seized.gov
Name Server: ns2.fbi.seized.gov
It is not known whether the FBI only seized the domains or also has access to the website’s content and server logs.
This action follows Handala’s massive cyberattack on US medical giant Stryker, in which they compromised a Windows domain administrator account and created a new Global Administrator account to use in their attack.
They then issued the Microsoft Intune “wipe” command to factory reset approximately 80,000 devices, including computers and mobile devices. Employees whose personal devices were managed by the company also found their devices wiped.
Handala has acknowledged the website seizures and need for more “resilient infrastructure,” stating that they are in the process of creating new websites to announce their attacks.
“In light of recent events and the need to establish secure and resilient infrastructure, we inform you that building a new digital base is a complex and time-consuming process,” reads a Telegram post from the group.
“However, we remain committed to continuing our mission without interruption.”
After the attack, Microsoft and CISA released guidance on hardening Windows domains and securing Intune to prevent similar attacks at other companies.


