
Hackers are exploiting a critical severity vulnerability, tracked as CVE-2026-3055, in Citrix NetScaler ADC and NetScaler Gateway appliances to obtain sensitive data.
Citrix initially disclosed CVE-2026-3055 in a security bulletin on March 23, alongside a high-severity race condition flaw tracked as CVE-2026-4368. The issue impacts versions of the two products before 14.1-60.58, versions older than 13.1-62.23, and those older than 13.1-37.262.
The vendor underlined that the flaw only affected appliances configured as a SAML identity provider (IDP) and noted that action is required only for administrators running on-premise appliances.
In response to the bulletin, multiple cybersecurity firms highlighted that CVE-2026-3055 has a significant risk, noting technical resemblance to the widely exploited ‘CitrixBleed’ and CitrixBleed2’ from 2023 and 2025, respectively.
watchTowr, a company that provides adversarial simulation and continuous testing services, said on Saturday that it observed reconnaissance activity targeting vulnerable instances and warned that in-the-wild exploitation was imminent.
The next day, the researchers confirmed that threat actors started leveraging the flaw since at least March 27.to extract authentication administration session IDs, potentially enabling a full takeover of NetScaler appliances.
“In-the-wild exploitation has begun, with evidence from our honeypot network showing exploitation from known threat actor source IPs as of March 27th,” reports watchTowr.
watchTowr’s analysis indicates that CVE-2026-3055 actually covers at least two distinct memory overread bugs, not one. The first affects the ‘/saml/login’ endpoint handling SAML authentication, while the second one affects the ‘/wsfed/passive’ endpoint used for WS-Federation passive authentication.
The researchers demonstrated that the security flaw can be leveraged to “sensitive information – including authenticated administrative session IDs.”
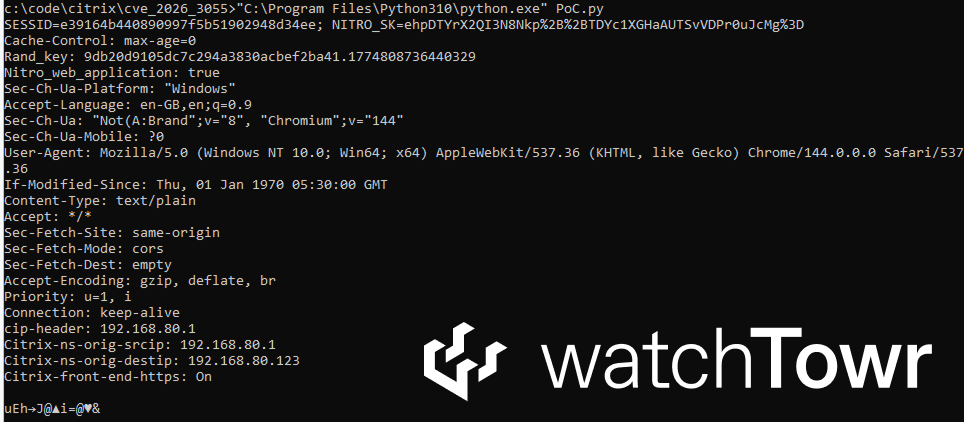
Source: watchTowr
The researchers call Citrix’s incomplete disclosure of the security issue in the security bulletin “disingenuous.” They also shared a Python script to help defenders identify vulnerable hosts in their environments.
As of publishing, Citrix’s bulletin does not mention CVE-2026-3055 being exploited. BleepingComputer has contacted the company for a comment on the reported threat actor activity targeting unpatched appliances, but we have not received a response.
As of March 28, The ShadowServer Foundation sees 29,000 NetScaler and 2,250 Gateway instances exposed online, although it is unclear what percentage of those are vulnerable to CVE-2026-3055.


