
The Seiko USA website was defaced over the weekend, displaying a message from attackers claiming they stole its Shopify customer database and threatening to leak it unless a ransom is paid.
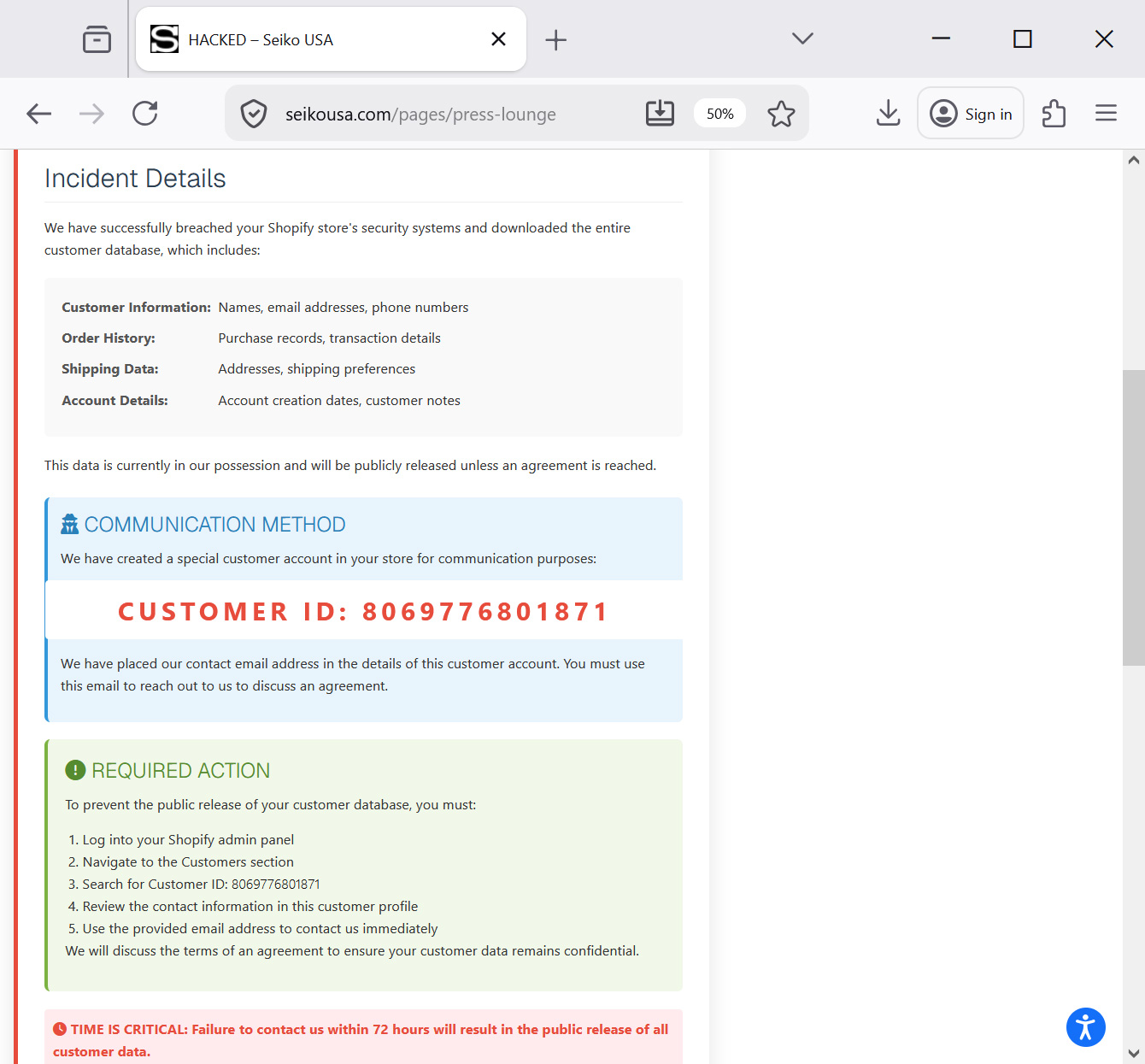
Visitors to the “Press Lounge” section of the site were shown a page titled “HACKED,” which replaced normal content with what appeared to be a ransom demand and data breach notification.
The message warned that attackers had gained access to the company’s Shopify backend and exfiltrated sensitive customer information.
“This is an urgent security notification regarding your Shopify store. Your customer database has been compromised,” read the defaced webpage.
“We have successfully breached your Shopify store’s security systems and downloaded the entire customer database.”
Source: BleepingComputer
The threat actors claim the stolen data contains the following information:
- Customer Information: Names, email addresses, phone numbers
- Order History: Purchase records, transaction details
- Shipping Data: Addresses, shipping preferences
- Account Details: Account creation dates, customer notes
The attackers warn that the stolen data will be publicly released unless Seiko USA enters into negotiations.
As part of the demand, they instructed the company to locate a specific customer account, identified as ID 8069776801871, within the Shopify admin panel. The threat actors say that a contact email address was added to that account profile and should be used to initiate negotiations.
The defacement further warned that Seiko USA had 72 hours to contact them or the alleged database would be published.
BleepingComputer has not been able to determine what threat actor is behind the attack and whether their claims are legitimate.
Seiko USA has not publicly confirmed or responded to BleepingComputer emails about the incident, but has since removed the extortion message from the website.
AI chained four zero-days into one exploit that bypassed both renderer and OS sandboxes. A wave of new exploits is coming.
At the Autonomous Validation Summit (May 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls hold, and closes the remediation loop.



