
The ShinyHunters extortion gang has breached education technology giant Instructure again, this time exploiting a vulnerability to deface Canvas login portals for hundreds of colleges and universities.
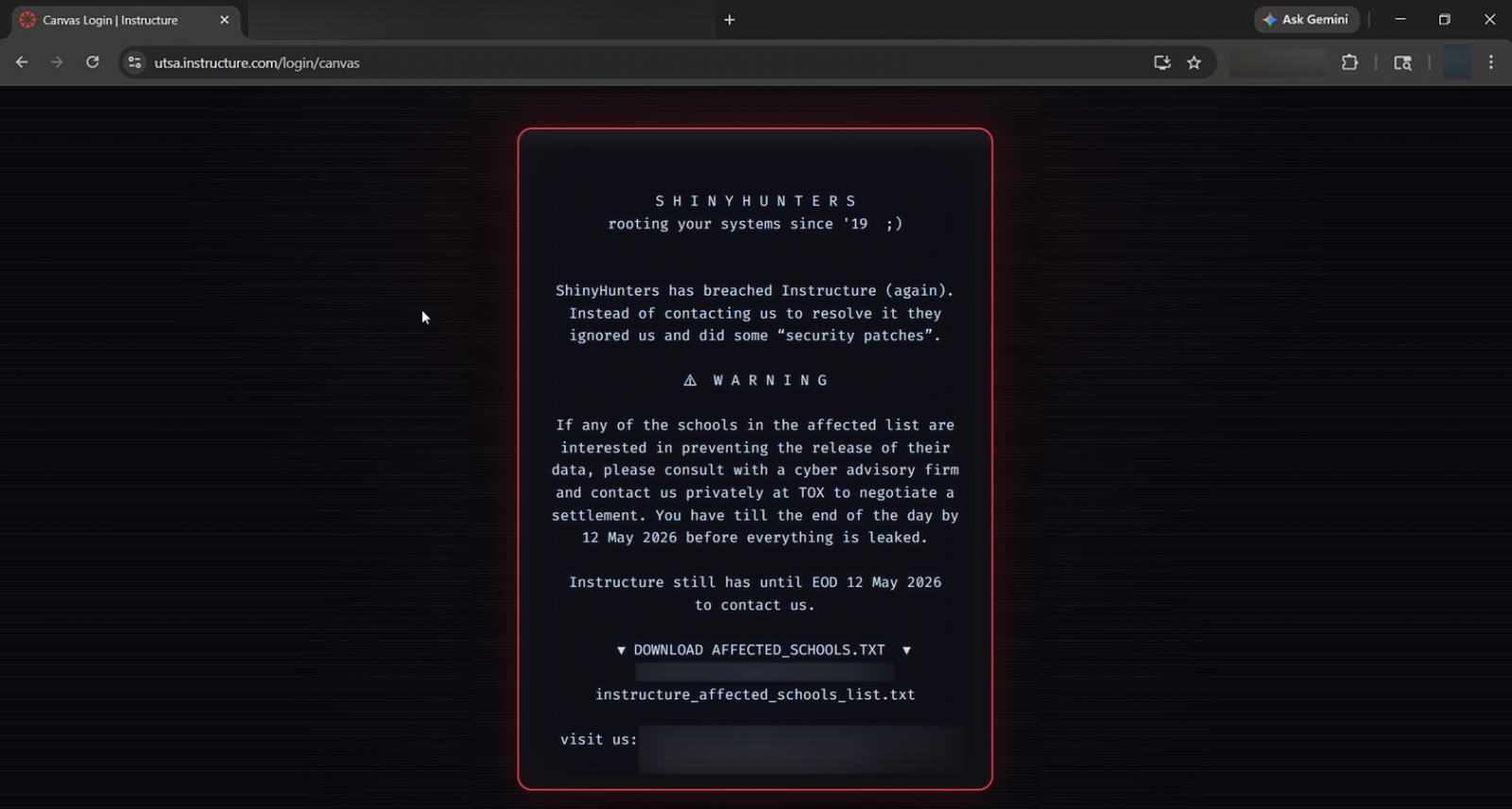
The defacements, which were visible for roughly 30 minutes before being taken offline, displayed a message from ShinyHunters claiming responsibility for the earlier Instructure breach and threatening to leak stolen data if a ransom is not paid.
The message warns that Instructure and schools have until May 12 to contact them to negotiate a ransom, or students’ data will be leaked.
“ShinyHunters has breached Instructure (again). Instead of contacting us to resolve it they ignored us and did some ‘security patches’,” reads the defacement.
“If any of the schools in the affected list are interested in preventing the release of their data, please consult with a cyber advisory firm and contact us privately at TOX to negotiate a settlement. You have till the end of the day by May 12 2026 before everything is leaked,” continued the message.
BleepingComputer has learned that threat actors defaced the Canvas login portals for approximately 330 educational institutions, replacing the standard login pages with an extortion message. This defacement message also appeared in the Canvas app.
The defacement was allegedly caused by a vulnerability in Instructure’s systems that allowed the threat actor to modify the login portals. Instructure has since taken Canvas offline while they respond to the latest cyberattack.
Last week, Instructure disclosed that it was investigating a cyberattack after threat actors claimed to have stolen 280 million student and staff records tied to 8,809 schools, universities, and education platforms using its Canvas learning management system.
The ShinyHunters gang later told BleepingComputer that the stolen data included user records, private messages, enrollment data, and other information allegedly gathered through Canvas data export features and APIs.
Instructure confirmed that data was stolen during the attack but that they are continuing to investigate the incident.
BleepingComputer has repeatedly contacted Instructure with questions about the attack, including today’s, and whether they plan on notifying students and staff about the data breach. However, our emails have so far remained unanswered.
Canvas is one of the most widely used learning management systems in higher education and K-12 environments, helping schools manage coursework, assignments, grading, and communication between students and faculty.
Who is ShinyHunters
The name ShinyHunters has long been associated with numerous threat actors who have conducted data breaches since 2018.
This year, threat actors using the ShinyHunters name have become among the most prolific groups conducting data theft and extortion attacks against companies worldwide.
Primarily focusing on Salesforce and other cloud SaaS environments, the threat actors are linked to a growing number of breaches involving companies such as Google, Cisco, PornHub, and online dating giant Match Group.
The extortion gang commonly breaches third-party integration companies and uses stolen authentication tokens to access connected SaaS environments and steal customer data.
The threat actors are also known for conducting voice phishing (vishing) attacks targeting Okta, Microsoft, and Google single sign-on (SSO) accounts, impersonating IT support staff to trick employees into entering credentials and multi-factor authentication (MFA) codes on phishing sites.
As BleepingComputer first reported, the ShinyHunters group has also recently adopted device code vishing attacks to obtain Microsoft Entra authentication tokens.
After stealing credentials and authentication codes, the threat actors hijack SSO accounts to breach connected enterprise services such as Salesforce, Microsoft 365, Google Workspace, SAP, Slack, Adobe, Atlassian, Zendesk, and Dropbox.
While members of the ShinyHunters gang are responsible for numerous attacks, they are also known to operate as an extortion-as-a-service group, conducting extortion on behalf of other threat actors in exchange for a share of ransom payments.
There have been numerous arrests linked to the ShinyHunters name, including suspects connected to the Snowflake data-theft attacks, breaches at PowerSchool, and the operation of the Breached v2 hacking forum.
Yet despite these arrests, companies continue to receive extortion emails signed with the message, “We are ShinyHunters.”
AI chained four zero-days into one exploit that bypassed both renderer and OS sandboxes. A wave of new exploits is coming.
At the Autonomous Validation Summit (May 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls hold, and closes the remediation loop.


